The network is the connections between all of the devices on a network and the devices used to connect to an internet service provider. From the service provider there is a connection to the internet backbone which is how you connect to all the websites that you visit. Security is important on the network because hackers may use your network to gain access to your devices and steal your information.
Wireless

If you have a wireless network, securing the wireless communications with the best encryption is important. The stronger the encryption the less chance your wireless network will be cracked. As of right now, the most secure wireless protocol is WPA2.
Access List
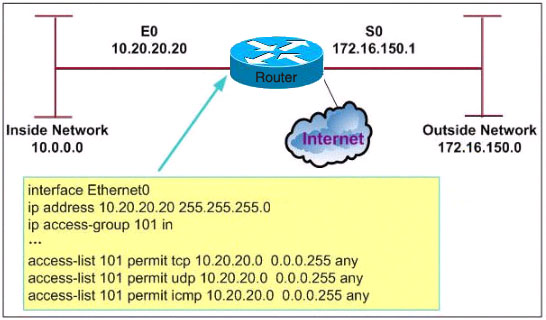
An access list is usually implemented on a router and/or wireless access point. You can set up an access list stating all the devices that can join the domain/network by their MAC address, NetBIOS name, machine name, or another identifier. You may also configure the access list to explicitly deny all new devices from connecting until that device is reviewed and white listed.
VPN
Configuring a vpn has many different uses. It encrypts all traffic between your machine and the vpn server. This means that all entities in between will not be able to see what types of traffic the user is sending and receiving.
If you would like to know more, please visit our company website VortexITsystems